- Saved searches
- Use saved searches to filter your results more quickly
- License
- jiripudil/otp
- Name already in use
- Sign In Required
- Launching GitHub Desktop
- Launching GitHub Desktop
- Launching Xcode
- Launching Visual Studio Code
- Latest commit
- Git stats
- Files
- README.md
- About
- Saved searches
- Use saved searches to filter your results more quickly
- danielbachhuber/one-time-login
- Name already in use
- Sign In Required
- Launching GitHub Desktop
- Launching GitHub Desktop
- Launching Xcode
- Launching Visual Studio Code
- Latest commit
- Git stats
- Files
- README.md
- About
- PHP Login with OTP Authentication
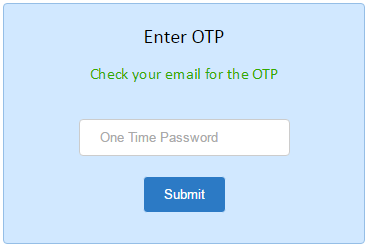
- Login form with OTP
- PHP Code to Validate OTP Authentication
Saved searches
Use saved searches to filter your results more quickly
You signed in with another tab or window. Reload to refresh your session. You signed out in another tab or window. Reload to refresh your session. You switched accounts on another tab or window. Reload to refresh your session.
PHP library that generates and verifies one-time passwords.
License
jiripudil/otp
This commit does not belong to any branch on this repository, and may belong to a fork outside of the repository.
Name already in use
A tag already exists with the provided branch name. Many Git commands accept both tag and branch names, so creating this branch may cause unexpected behavior. Are you sure you want to create this branch?
Sign In Required
Please sign in to use Codespaces.
Launching GitHub Desktop
If nothing happens, download GitHub Desktop and try again.
Launching GitHub Desktop
If nothing happens, download GitHub Desktop and try again.
Launching Xcode
If nothing happens, download Xcode and try again.
Launching Visual Studio Code
Your codespace will open once ready.
There was a problem preparing your codespace, please try again.
Latest commit
Git stats
Files
Failed to load latest commit information.
README.md
OTP is a library that generates and verifies One-Time Passwords conforming to the HOTP (RFC 4226) and TOTP (RFC 6238) algorithms. These one-time passwords are commonly used as a second factor during user authentication. In short, your application and the user’s OTP application are both able to generate a number based on a shared secret. Whenever you need to authenticate the user, ask them to enter the code generated by their application and verify it with this library.
Installation and requirements
$ composer require jiripudil/otp
The entrypoint of this library is the JiriPudil\OTP\OTP class:
$otp = new JiriPudil\OTP\OTP('My Application', $otpType);
It expects you to provide:
- The $issuer name. This is often used by the end-user applications to distinguish OTPs for various services, and should thus clearly identify your application.
- An $otp type. This library provides implementations for both HOTP and TOTP. See below for details.
- The hashing $algorithm . This is optional and defaults to SHA-1. ⚠ Please be aware that some end-user implementations such as Google Authenticator only support this algorithm.
The JiriPudil\OTP\TimeBasedOtp class implements the TOTP according to RFC 6238 and it is perhaps the most commonly used type of OTPs. It generates a code in a fixed-time interval that defaults to 30 seconds. ⚠ While the interval can be changed, again, some end-user implementations do not support different intervals than the default.
Using time-based OTPs requires the clocks on your server and in the user’s application to be in sync. To compensate for the possible differences between the times, you can provide an optional $tolerance which determines how many time periods before and after the current time should be considered valid. It defaults to 1, which means that the code for the previous and the next period will pass the verification.
$otpType = new JiriPudil\OTP\TimeBasedOTP();
The JiriPudil\OTP\HmacBasedOTP class implements the HOTP according to RFC 4226. Instead of time, this type of OTP relies on a counter that is kept both by the user’s application and by the server. That’s why the class requires you to provide an implementation of a JiriPudil\OTP\HmacBasedOTP\CounterRepository which retrieves and updates the counter for a given $account . Your implementation should operate upon some persistent storage such as a relational database.
The user’s counter is incremented every time they request a new code, while the server’s counter is only incremented after a successful verification attempt. To account for a possible desynchronization of the counter value, you can configure a $lookAhead parameter which tells this library to check several subsequent counter values. This parameter defaults to 3.
$otpType = new JiriPudil\OTP\HmacBasedOTP($myCounterRepository);
First of all, you need to generate a random secret. The OTP class provides a method for that which makes sure that the secret is long enough for the configured hashing algorithm:
$secret = $otp->generateSecret();
The secret must be unique to the user, and should therefore be stored somewhere with other user data – preferably encrypted because it is a very sensitive value:
$myUserRepository->encryptAndSaveOtpSecret($myUser, $secret);
A second value that is tied to the user is the account name: this should be a value that uniquely identifies the user in your application, e.g. their email address. These two pieces of information are exposed to this OTP library in the form of JiriPudil\OTP\Account\AccountDescriptor . There is a handy simple implementation in JiriPudil\OTP\Account\SimpleAccountDescriptor which should be sufficient for most cases:
$account = new SimpleAccountDescriptor($myUser->getEmailAddress(), $myUser->getOtpSecret());
You can then call getProvisioningUri for this $account to retrieve a URI that can be used to set up the end-user OTP application. You can optionally specify the number of digits the generated code should have – this can be a value between 6 and 8 inclusive, and it defaults to 6 which is the most commonly used value:
$uri = $otp->getProvisioningUri($account, digits: 6);
This URI is usually displayed in the form of a QR code that the user application can scan. Alternatively, you can directly display the Base32-encoded secret for the user to type or copy into their application:
$encodedSecret = $account->getSecret()->asBase32();
Once the user has set up the account in their OTP application, you can ask them to enter the code and easily verify that the setup is correct:
if ($otp->verify($account, $enteredCode, expectedDigits: 6)) < // successfully verified > else < // incorrect code >
At this point, you should generate and display a set of recovery codes in case the user loses access to their OTP application. After that, you can consider the user’s OTP setup in your application finished, and you can start requiring the code as a second factor during their authentication.
This package can also be used as an OTP client:
$code = $otp->generate($account, digits: 6);
About
PHP library that generates and verifies one-time passwords.
Saved searches
Use saved searches to filter your results more quickly
You signed in with another tab or window. Reload to refresh your session. You signed out in another tab or window. Reload to refresh your session. You switched accounts on another tab or window. Reload to refresh your session.
Generate a one-time login URL for any user
danielbachhuber/one-time-login
This commit does not belong to any branch on this repository, and may belong to a fork outside of the repository.
Name already in use
A tag already exists with the provided branch name. Many Git commands accept both tag and branch names, so creating this branch may cause unexpected behavior. Are you sure you want to create this branch?
Sign In Required
Please sign in to use Codespaces.
Launching GitHub Desktop
If nothing happens, download GitHub Desktop and try again.
Launching GitHub Desktop
If nothing happens, download GitHub Desktop and try again.
Launching Xcode
If nothing happens, download Xcode and try again.
Launching Visual Studio Code
Your codespace will open once ready.
There was a problem preparing your codespace, please try again.
Latest commit
Git stats
Files
Failed to load latest commit information.
README.md
Contributors: danielbachhuber, aaronjorbin, acali, gdespoulain
Tags: login
Requires at least: 4.4
Tested up to: 5.8
Stable tag: 0.4.0
Requires PHP: 7.4
License: GPLv2 or later
License URI: http://www.gnu.org/licenses/gpl-2.0.html
Use WP-CLI to generate a one-time login URL for any user
Need access to a WordPress install but don’t want to create a new user account? Use this plugin to generate one-time login URLs for any existing user. Then, copy the URL, paste it into your web browser, and. voila!
Because they are one-time login URLs, they will only work once. If you need access again, you’ll need to run the WP-CLI command again.
Using WP CLI to generate OTT URLs
wp plugin install one-time-login --activate && wp user one-time-login --count=3 --delay-delete After you run the command above, you’ll see a success message like this:
http://wpdev.test/wp-login.php?user_id=2&one_time_login_token=93974b48e3a418b895fc7ca476f1a607d8b99345 Or like this if you asked for more than one:
http://wpdev.test/wp-login.php?user_id=1&one_time_login_token=2b9c6f5d71d51d530e397ee9da3b50e4e3dd06e7 http://wpdev.test/wp-login.php?user_id=1&one_time_login_token=90897da439a116c613fc1c49c372e6b1f7c72ad8 http://wpdev.test/wp-login.php?user_id=1&one_time_login_token=68c8074743de849db606500c3caa39a7432dc601 - count: Generate more than one login token (default: 1);
- delay-delete: Delete existing tokens after 15 minutes, instead of immediately.
Using WP API to generate OTT URLs
curl -X POST \ http://wpdev.test/wp-json/one-time-login/v1/token -H 'authorization: Basic YWRtaW46eFRQeUJ5c3hEckhkY3BNYjE2endiQ2tj' -H 'cache-control: no-cache' -H 'postman-token: 8dcfa79a-401a-2c7d-c593-703e683ce785' -d '< "user":"admin", "count": 3, "delay-delete": true >' Just as with WP CLI, you can add the count and delay_delete parameters to your call.
Feel free to file issues and pull requests against the project on Github.
See description for installation and usage instructions.
- Introduces —delay-delete flag to delete old tokens after 15 minutes instead of immediately.
- Improves invalid token message when user is already logged in: «Invalid one-time login token, but you are logged in as ‘user_login’. Go to the dashboard instead?».
- Introduces support for multiple one-time login links.
- Links to the login screen from the «Invalid token» error message.
- Fires one_time_login_created action when login URL is created, and one_time_login_logged_in action when user is logged in via one-time login URL.
About
Generate a one-time login URL for any user
PHP Login with OTP Authentication
Login with an OTP code is a secure method for the user authentication process. In this method, a one-time password is generated dynamically and sent to the user who attempts login.
OTP can be sent to the user’s email or his mobile phone. When the user enters the OTP code then the application will authenticate the user via this code.
In this tutorial, we are going to see an example to authenticate user login via an OTP code using email . In a previous tutorial, we have already seen a PHP code for login with username and password.
In this example, when the registered user enters email to login, an OTP code is sent to the email address. Using this OTP code the user will be validated. Once the user uses this code then it will be invalid, meaning it cannot be used again. Also, this token will be valid for a day, then it will be expired.
Login form with OTP
The following code shows login form to the user to enter his email address. On entering email, it shows an input to enter the OTP code sent to his email address. After submitting OTP, PHP will validate the code and show authentication result to the user.